Internet of Things (IoT) devices with high definition technology allow them to interact with the internet and can be managed remotely. These devices are integrated with technology like sensors and functional software that allows the machine-to-machine interaction. The insecure IOT devices provide an easy gateway for cybercriminals to get inside the network. The enterprise use of IoT includes industry-specific devices used in healthcare and devices used in industries like smart security systems. This industrial IoT will involve a combination of sensors, Wi-Fi networks, big data, and data analytics to optimize processes.
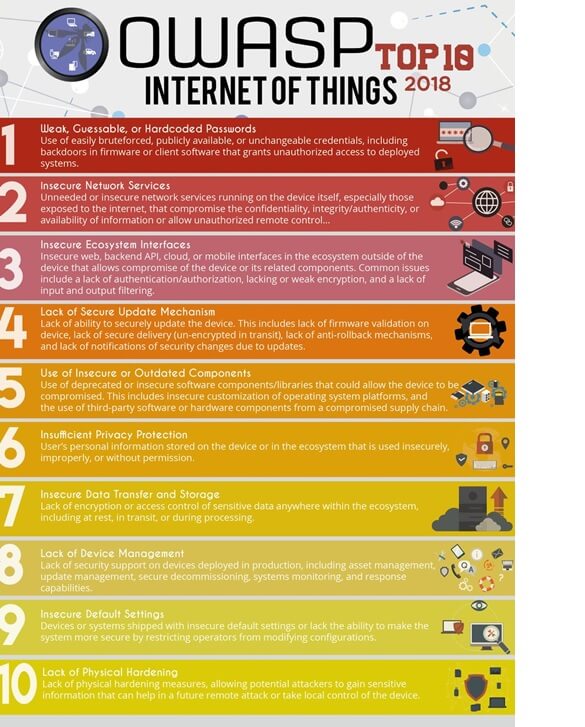
Last week we read about the IoT security challenges and efforts such as OWASP Top 10 IoT Security project (2018) that provides basic level guidelines for device manufactures and developers to create secure solutions.
I looked at a couple of IoT security technologies in the market and tried to understand the foundation of those technologies. Below are e-InnoSec team thoughts in brief.
- Inventory –In order to secure the IoT environment, corporations need to know the inventory of devices and the type of devices in use. This also means an automated way of identifying devices in the domain.
- Classification of inventory – Inventory is further classified in types and business functions it performs.
- Assess the risk – Risk assessment is the beginning of the process.
Below is the list of a few devices that support the expansion of the internet beyond computers.
| Nest Smoke AlarmNest Learning ThermostatRing DoorbellGoogle Home Voice ControllerAmazon Echo | August Doorbell CamAugust Smart LockBelkin WeMo Smart Light SwitchFootbot Air Quality MonitorPhilips Hue Bulbs |
The organizations and people in their homes connect the devices to the network. But if the device is not secured properly and is discoverable on the network then it can be an easy gateway for hackers.
The enterprise use of IoT includes industry-specific devices used in healthcare and devices used in industries like smart security systems. This industrial IoT will involve a combination of sensors, Wi-Fi networks, big data, and data analytics to optimize processes.
One of the biggest issues with IoT is security and the sensors collecting data that are capable of transferring data across networks and to manufacturers. The basic design of some of the IoT devices lacks security considerations such as encryption of data in transit and at rest. The risks of espionage, vandalism, theft, misuse, hacking, and fraud are higher when industrial machinery connects to IoT networks. The software flaws and lack of capability to be patched could even increase the risk higher. There is also compliance risk with privacy and private healthcare data.
Below are the five infamous IoT Hacks:
- The cyber attack related to the Mirai DDoS botnet
- A data breach related to a children’s toy
- The Devil’s Ivy Rube-Goldberg attack
- Wi-Fi baby hard monitors
- Virtual carjacking
The OWASP Top 10 IoT Security project (2018) provides basic-level guidelines for device manufactures and developers to create secure solutions (refer Figure 1). The consumers and organizations also need to ensure security considerations are important while selecting and deploying devices. Here are some guidelines for organizations:
- Updating BYOD policy to include IoT devices and provide a listing of approved IoT devices
- Research and approval process for IoT devices
- Using a strong encryption method for Wi-Fi
- Limiting the use of Wi-Fi for approved IoT devices
- Use of the isolated network for IoT systems
- Use of strong and unique passwords and renaming the devices
- Hardening devices following vendor instructions
- Updating software immediately after release
- Avoid the use of public Wi-Fi networks
- Use of multifactor authentication if available
The 2018 release of the OWASP IoT Top 10, which represents the top ten things to avoid when building, deploying or managing IoT systems (https://www.owasp.org/index.php/OWASP_Internet_of_Things_Project).